For your online accounts, passwords are the weakest point in any level in security. If someone accesses your credentials, your content and your vital information are at risk.

The goal of the game Password is to get your partner to guess the password by giving him a one word and only one word clue. Password Game Rules & How to play it Divide yourself into 2 teams Team A and Team B. In each round one of the members from each team will be given a password. The objective of the game is to make your partner guess. The word 'passphrase' is used to convey the idea that a password, which is a single word, is far too short to protect you and that using a longer phrase is much better. The increased length can allow for a greater number of possibilities overall, even if you use a passphrase made of random words to help you remember it. If you click the words under the image, it will take you to the post with instructions on how to use the printable. Hopefully this page can help you find the game you’re looking for. Here’s some various word lists I’ve made that you can print out and cut up. Before the game begins, players take turns writing 5 to 10 words on individual slips of paper. These words become the “passwords” used during game play. Each team selects a player to be It for each round, while teams pick a password from the opposite team’s word bank. It stands before his team as they share the password with. Use our Word List feature to build your own Word Search, Cross Search, and Jumbled Word worksheets to print for your children/students, or create interactive vocabulary games - Hangman, Multi Word Scramble, Blackberry Game, Telephone Game, or Word Flash. Assign these fun activities to your students with our Virtual Classroom.
Although most websites today offer extra security protection, anyone who retrieves or guesses your password can easily bypass other security measures that most sites have in place.
That person can make any changes to your online accounts, make purchases, or otherwise manipulate your data. Always have your data backed up just in case.
Selecting a secure password is crucial because let’s face it, our entire life is now spent in the digital universe: social media, banking, email, shopping, and more.
Many people have the terrible habit of using the same passwords across multiple accounts. It may be easier to remember, but if there is a security vulnerability on one account, everything could be compromised.
Passwords are Your Digital Keys
Your sign-on details are the digital keys to all your personal information and the best way to keep your company information safe. You want to make sure to keep your passwords safe from third-parties so that they can stay private.
While many small-time cybercriminals attempt to hack into email accounts and social networks, they often have darker and more malicious goals. They’re usually after information from personal finances such as credit card details and bank account info, or business accounts to either directly line their pockets or attempt to extort an individual or business.
The two significant security risks are insecure password practices and shared accounts. This involves using the same password for personal and business apps, reusing passwords across multiple apps, sharing passwords with other employees, and storing passwords insecurely.
The point here is that a robust and secure password is all that could potentially stand between you and pesky cybercriminals.
How Can Your Password Be Compromised?
Outside of spyware and phishing attacks, there are numerous techniques that hackers use to crack your passwords.
One strategy is to gain access is by straight-up guessing your password. They could do this by looking at your security questions, your social media presence, or any other found information that could be online. That is why it is vital that not to include any personal information in your passwords.
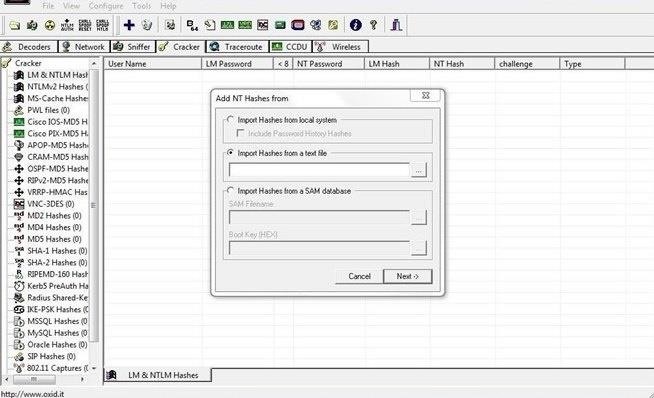
Other tactics that hackers utilize is to try a password cracker. By using brute force, a password cracker employs various combinations continuously until it breaks the password and gains access to the account. We’ve all seen this in the movies, but it’s worth noting that this is not just a Hollywood special effect.
The less complex and shorter your password is, the faster it can be for the tool to produce the correct combination of characters. The more complex and more extended your passwords are, it is less likely the hacker will use a brute force technique. That is due to the extended amount of time it would take for the software to figure it out.
Instead, they will put in place a method called a “dictionary attack.” Here is where a program will cycle through common words people use in passwords.
Strong Password Ideas and Tips with Great Examples
- Make sure you use at minimum ten characters. That is where it can get tricky. As previously noted, you should avoid using personal information or your pet’s information — those are the first choices for hackers to try and exploit. In determining your password strength, pay close attention to two significant details: the complexity and length you choose. Long-tail, complex passwords are tough to crack. To create complex but memorable passwords, use different types of characters, a mixture of lower and uppercase letters, symbols, and number
- Do not use directly identifiable information. The ones trying to hack into your accounts may already know personal details such as your phone number, birthday, address, etc. They will use that information as an aid to more easily guess your password.
- Use a unique password for each separate account. If you use the same password across multiple accounts, you could use the most reliable password possible, and if one account is compromised: all of them are. The recommended best practice is to create a strong password ideas list and use it for all your online accounts. Your unique list of passwords should be kept safe.
- Avoid common dictionary words. This mistake is the toughest one to avoid. The temptation is always there to use ordinary, everyday dictionary words. It is true that the most common password used today is, “password.” Avoid plain dictionary words as well as a combination of words. For instance, “Home” is a bad password. However, adding “Blue Home” isn’t an improvement either. A strong hacker will have a dictionary-based system that cracks this type of password. If you must use a single word, misspell it as best as you can or insert numbers for letters. Use a word or phrase and mix it with shortcuts, nicknames, and acronyms. Using shortcuts, abbreviations, upper and lower case letters provide easy to remember but secure passwords.
For example:
- “Pass Go and collect $200”– p@$$GOandCLCt$200
- “Humpty Dumpty sat on a wall” — humTdumt$@t0nAwa11
- “It is raining cats and dogs!”– 1tsrAIn1NGcts&DGS!
Incorporate emoticons, emoticons are the text format of emojis, commonly seen as various “faces.”
You may also find remembering a sentence for your password if it refers to something easy for you, but complex for others, such as; “The first house I ever lived in was 601 Lake Street. Rent was $300 per month.” You could use “TfhIeliw601lS.Rw$3pm.” You took the first letters of each word, and you created a powerful password with 21 digits.
If you want to reuse passwords across numerous accounts, this technique is particularly useful as it makes them easy to remember. Even though, as already mentioned, you really should use separate passwords, you can customize each per account. Utilizing the same phrase as above, “Humpty Dumpty sat on a wall” we created a secure and reliable password, and now you can use it on Amazon, Netflix, or Google accounts:
Here are good password examples using this technique.
- AMZn+humTdumt$@t0nAwa11
- humTdumt$@t0nAwa11@gOoGL
- humTdumt$@t0nAwa114netFLX
Weak Passwords to Avoid
Everyone is guilty of creating easy to guess passwords at some point in their digital life. You might feel confident that when you chose “3248575” that no one would figure out is your phone number. The examples below add to what are weak passwords that at first appear strong. However, once you look a little closer, you realize what is missing.
A brief explanation of what makes these bad choices follows each:
- 5404464785: Using numbers such as these quickly reveal someone’s phone number. By using this strategy, you are breaking two basic rules, using personal information and all numbers.
- Marchl101977: The birthday password. Even though this password contains a combination of numbers with small and capital letters and is over ten characters long, it is a disaster waiting to happen. It too breaks the rules by starting with a standard dictionary word, use of personal information and it lacks special characters.
- P@ssword234: You may at first feel this password meets the basics. However, it indirectly fails our tests. While it does have over ten characters, contains special characters and numbers, a mix of the letters, and it does not include any personally identifiable information, it is still considered weak. Because of how easy they are to guess, replacing letters for symbols is not a strong recommendation. It also offers the standard “234” sequential pattern.
What is Two-Factor Authentication?
“Multi-factor authentication” in the digital world is simply an extra layer of security. As common as it may seem in the technology industry, if you ask around, you will find that not everyone knows about “Two Factor Authentication”. What’s even more interesting is that many people who don’t understand the term may very well be using it every day.
As mentioned throughout this blog, standard cybersecurity solutions and procedures only require a necessary username and password. With such simplicity, criminals score by the millions.
Two Factor Authentication, also known as 2FA, is two-step verification process, or TFA. It requires more than just a username and password but also something that only that user has on them.
That could be a document or piece of information only they should know or immediately have on hand, like a token of some type. Using this technique makes it difficult for cybercriminals to gain access and steal the identity or personal information of that person.
Many people do not understand this type of security, and they may not recognize it though they use it on a daily basis. When you use hardware tokens, issued by your bank to put to use with your card and PIN when needing to complete internet banking transactions, you’re using 2FA.
They are merely utilizing the benefits of multi-factor authentication by using something they have or what they know. Putting this process to use can indeed help with lowering the number of cases of identity theft on the web, as well as Phishing through email. The reason is that it needs more than supplying the mere name and password details. See our article on preventing ransomware for more information.
There are downsides, however. New hardware tokens which come from the bank in the form of card readers or key fobs that require ordering may slow business down. There can be issues for customers waiting and wanting to gain access to their private data through this authentication procedure.
The tokens get easily lost because they are small, so that too causes problems for everyone when a customer calls in requesting new ones. Tokenless Authentication is the same procedure except there no tokens involved. It is quicker, faster, and less expensive to establish and maintain across numerous networks.
Managing Passwords the Easy Way
Implementing enterprise password management helps small, and large businesses keep their information sound. No matter how many employees you have, they need help protecting the passwords that operate your business and your private life.
A password manager helps you generate strong passwords as well as remembering each one for you. However, if you do choose this route, you will need to at least create a secure password and remember it.
With the masses of websites for which you have accounts, there is no logical way to remember each one easily. Trying to remember every single password, (and where you wrote them down) and not duplicate one or resorting to using an easy-to-read pattern, is where the trouble starts.
Here is where password managers make life more comfortable – as long as you can create a strong master password that is necessary for you to remember. The good news is, that is the last one you will you need to worry about no matter how many accounts you have.
The Truth about Browser-Based Managers
Web browsers – Safari, Firefox, Chrome, and others – each have integrated password managers.
No browser can compete with a dedicated solution. For one, Internet Explorer and Chrome store your passwords in an unencrypted form on your computer.
People can easily access password files and view them unless you encrypt your hard drive. Mozilla Firefox has the feature, “master password” that with one single, “master password” you can encrypt your saved passwords. It then stores them in an encrypted format on your computer.
However, Firefox password manager is not the perfect solution, either. The interface does not help you generate random passwords, and it also lacks various features such as cross-platform syncing.
There are three standout-above-the rest dedicated platforms for password management. Each of these is a reliable option, and the one you choose will rely on what is most important to you.

- KeePass
The important part is remembering that you need to use genuinely random words for a secure password. A great example is “cat in the hat” would make a horrible word because it is a common phrase and makes sense. “My beautiful red car” is another type that is horrible.
However, something such as “correct kid donor housewife” or “Whitehorse staring sugar invisible” are examples of a randomized password. They make no sense together and are in no grammatically correct order, which is fantastic. Managers also allow users to store other data types in a secure form–everything from secure notes to credit card numbers.
In Closing, Stay Secure and Protected
We are experiencing times when passwords that you can remember is not enough to keep yourself and your company safe. If you do suspect criminal mischief with your account, immediately change your passwords.
Doing so only takes a minute, as restoring your personal life and your company financial records and history can often be devastating. Follow the steps listed above for selecting a strong unique password to establish and maintain safe accounts, secure email, and personal information. If your password is easy to remember, it is probably not secure.
Recent Posts
Create strong passphrases with EFF's new random number generators! This page includes information about passwords, different wordlists, and EFF's suggested method for passphrase generation. Use the directions below with any set of dice.
And now, a message from internationally renowned security technologist, author, and EFF Board Member Bruce Schneier:
Directions
We’ll walk you through how to use EFF's Long Wordlist [.txt] to generate a passphrase. For most applications, we suggest making a six-word passphrase.
Step 1: Roll five dice all at once. Note the faces that come up without looking at the wordlist yet. (On our dice, the EFF logo is equivalent to rolling a one.)
Step 2: Your results might look like this reading left to right: 4, 3, 4, 6, 3. Write those numbers down.
Step 3: Open EFF's Long Wordlist [.txt] to find the corresponding word next to 43463.
Step 4: You will find the word 'panoramic.' This is the first word in your passphrase, so write it down.
Step 5: Repeat steps 1-4 five more times to come up with a total of SIX words.
When you are done, your passphrase may look something like this:
panoramic nectar precut smith banana handclap
Step 6: Come up with your own mnemonic to remember your phrase. It might be a story, scenario, or sentence that you will be able to remember and that can remind you of the particular words you chose, in order. For example:
The panoramic view, as I tasted the nectar of a precut granny smith apple and banana, deserved a handclap.
This passphrase is one of 221073919720733357899776 (or about 2⁷⁷) alternatives that could have been chosen by this method. With so many possibilities, this passphrase will be very hard to guess by brute force.
Why Use Passphrases?
The word 'passphrase' is used to convey the idea that a password, which is a single word, is far too short to protect you and that using a longer phrase is much better. The increased length can allow for a greater number of possibilities overall, even if you use a passphrase made of random words to help you remember it. Passphrases made of randomly-chosen words can be both easy to remember and hard for someone else to guess, which is what we want out of a passphrase. While the EFF random number generators are not casino-grade dice, we believe that they are sufficiently random for these purposes.
Computers are now fast enough to quickly guess passwords shorter than ten or so characters - and sometimes quite a few more. That means short passwords of any kind, even totally random ones like nQm=8*x or !s7e&nUY or gaG5^bG, may be too weak, especially for settings where an attacker is able to quickly try an unlimited number of guesses. This is not necessarily true for an online account, where the speed and quantity of guesses will be limited, but it could be true in other cases (for instance, if someone gets ahold of your device and is trying to crack its encryption password).
When to Use a Passphrase
Your passphrase is especially suitable when directly used to encrypt information, like for full-disk encryption on your laptop or mobile device. The large number of possibilities makes it much harder for someone to crack even if they get ahold of your device and use encryption-cracking hardware. Other great uses are the passphrase for an encryption key (like your PGP or SSH key), or, especially, for unlocking a password safe or password manager application.
Your passphrase should only be used for a single purpose, and especially should not be used for more than one online account. Sometimes password databases or websites get compromised. If you reuse a passphrase and it ends up being leaked in a data breach or otherwise discovered, it can be used to try to access your other accounts.
Notes on Using the Different Wordlists
EFF's new long list, referenced in the directions above, is designed for memorability and passphrase strength. We recommend selecting a minimum of six words from our long wordlist, or when using any other list of this size. The more words you use, the stronger the passphrase. Different wordlists may produce passphrases with different degrees of memorability, but you don't get a significantly different passphrase strength by using one wordlist over another, if the lists are the same length.
When using one of our short wordlists (which contain 1296 words), roll only four dice at once. You can follow our passphrase-generating instructions above, using four dice instead of five. As mentioned elsewhere, passphrases created using one of the short wordlists might be easier to remember and type, but don't provide as much strength per word.
EFF's Long Wordlist [.txt], for use with five dice
EFF's Short Wordlist #1 [.txt], featuring only short words, for use with four dice
EFF's Short Wordlist #2 [.txt], for use with four dice, featuring longer words that may be more memorable.
Password The Game Word List Free
The creator of our wordlists, Joseph Bonneau, has written a deep dive about passphrase security, and the methodology and criteria he used to create our EFF wordlists. You can also use Arnold G. Reinhold's Dicewareword list, the original and still very popular list for using dice to create passphrases.
What Next?
Password The Game Word List Printable
Learn about password managers! These are a great way to avoid the pitfall of reusing passwords and passphrases. You can use the long, random passphrase that you've created today to protect an entire database of login information that your computer can remember so you don't have to. This makes it straightforward to use a different password for every online account, which is good security practice. Visit the password manager overview on EFF's Surveillance Self-Defense guide to learn more!
Good Words For Password Game
Your passphrase that protects a password vault is now a very important key! Forgetting this passphrase is also a serious risk which could result in permanently losing data, and some people might thus prefer to have the passphrase written down, especially while first trying to memorize it or if they won't be using it every day - but if so, it should be kept in a safe place, not in the same place where the data it protects will be stored. What counts as a safe place for you depends on what you anticipate might happen. It's safer to write on a single thickness of paper on a hard surface to avoid leaving an imprint of the passphrase.